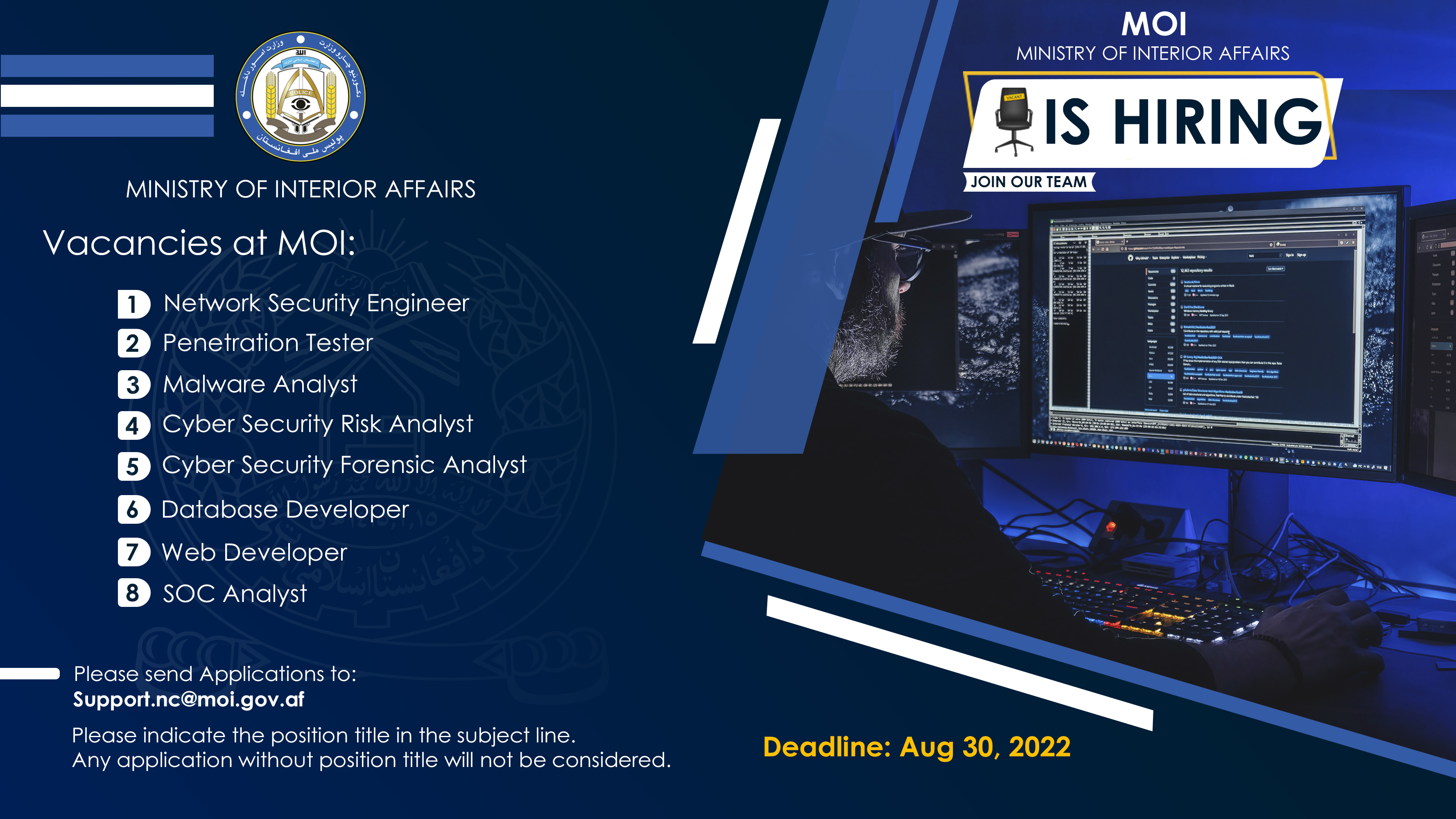
Vacancies at Ministry of Interior Affairs Afghanistan
Publish Date
Closing Date
Location
kabul
Job Title
Cyber Security Forensic Analyst
Required Skills
• Identify unusual files, scripts, configurations, and user activities based on bulk aggregation via an Endpoint Detection and Response (EDR) or triage tools, deployed at scale.
• Perform forensic data collections and basic forensic analysis in both on site and remote capacity.
• Coordinate directly with legal team/client IT departments to understand project scope.
• Maintain forensic tools set by staying current on version updates and new options in the market.
• Work closely with project management and other team members on completing complex projects in a fast pace, deadline driven environment.
• Assist in developing, documenting, and refining procedures to accomplish discovery process requirements.
• Manage all chain of custody best practices associated with the rules of evidence.
• Consistently adhere to standard operating procedures.
• Familiar with what routine OS activities and common software/user behavior looks like in the context of forensic artifacts or timelines.
• Understand common categories and formats of host-based indicators of compromise (IOCs) and how/where they can be leveraged to identify known-bad files/activity on an endpoint.
• Identify potentially malicious file system objects for deeper analysis.
The Desirables...
• Certified CHFI
___________________________________________________________________________
Job Title
Database Developer
Required Skills
• Strong understanding of database structures and practices.
• Experience in SQL database management and related products from Microsoft.
• Extensive experience designing, writing and troubleshooting complex queries, stored procedures, functions, tables, and indexes.
• Must have experience with the creation ETL processes, SSIS and SSRS.
• Must be able to troubleshoot complex queries, initiate T-SQL performance tuning and query optimization.
• Experience with data warehouse and automation.
• Experience in cloud database technologies like Azure SQL is a plus.
• Must have strong attention to detail and analytical skills.
• Work with developers to troubleshoot application problems related to the database.
• Understand and implement test scripts and plans, assess results and identify effective data conversion solutions.
• Identify and write performance tuning scripts and tools to efficiently extract and process large data sets.
The Desirables...
• Experience in SQL server installation, configuration and patching
• Knowledge of High Availability solutions (Replication, Always On or Log Shipping)
• Technical documentation skills
• Ability to work within a team environment
• Familiar with upgrades, migrations, backup and recovery options
• Able to implement the best database security practices
• Any prior programming knowledge is a plus
___________________________________________________________________________
Job Title
Malware Analyst
Required Skills
• Familiarity with Linux OS/Android OS
• Demonstrated knowledge in dynamic and static analysis and tools such as IDAPro and Ollydbg
• Familiarity with analyzing disassembly of x86 and x64 binaries
• Possess basic programming and scripting skills (e.g. .Net, Perl, Java, or Python)
• Familiarity with Kill Chain for incident response
• Familiarity with security technologies such as IDS, IPS, and HBSS
• Deep domain knowledge on Threat Intelligence
• Ability to setup collection mechanisms for malware samples (honey pots)
The Desirables…
• Cybersecurity certifications (e.g. CISSP, CEH, Security+, CREA)
• Reverse-engineering of Malware
___________________________________________________________________________
Job Title
Network Security Engineer
Required Skills
• Maintaining LAN, WLAN and Cloud services as per the business policy
• Develop secure system baseline configurations for Network systems.
• As a precautionary measure, analysis, recommend, and implement new security protocols for greater efficiency against any threat or malfunctions.
• Generating and maintaining the virtual private network (VPN), firewalls, web protocols security decorum.
• Reporting the security analysis of findings.
• Knowledge of performing routing protocols (MPLS, HAIPE/IP, QOS and WAN).
• Monitoring of web security gateway, perimeter security, network access controls, endpoint security.
• Work with technical leadership to define overall security technology, standards, and strategy.
• Monitor and remediate all security Incidents using vulnerability and security tools and scripting.
• Respond to security incidents and report on incident handling and resolution.
• Provide guidance and assistance with infrastructure design to ensure all security requirements.
• Manage Network, Cloud, and Remote Vulnerability Management tools.
• Recommend and Implement Security Solutions.
• Strong planning and organizing skills including the ability to manage several work streams simultaneously.
• Clear decision-making ability with the facility to judge complex situations and assess when to escalate issues.
___________________________________________________________________________
The Desirables…
• Certified CISSP
• Certified CISM
Job Title
Penetration Tester
Required Skills
• Familiarity with Linux administration.
• Scripting in python, bash / Unix tools.
• Web application development (any language).
• Networking – routing and diagnostics, firewalls.
• Vulnerability discovery, scanning, testing.
• Log analysis and SIEM.
• Web server and desktop security solutions – e.g. WAF, RASP, EDR.
• Knowledge of emerging security techniques, vulnerabilities, and approaches.
• Knowledge across a variety of platforms, operating systems and networked environments.
• Experience with penetration testing frameworks, tools and methodologies.
• Experience across security assurance activities.
The Desirables…
• Experience participating in hacking challenges.
• Proficiency with programming or scripting languages
• Relevant industry certifications (CREST, OSCP, etc.)
___________________________________________________________________________
Job Title
SOC Analyst
Required Skills
• Monitor a wide variety of information and network systems that include Circuits, LAN/WAN systems, routers, switches, firewalls, VoIP systems, servers, storage, backup, operating systems and core applications.
• Will be responsible for the uptime of the various client projects being managed /monitored.
• Regularly examine multiple monitoring systems for unexpected deviations.
• Should be responsible of level 1 troubleshooting of Backup, Server and Network related issues.
• performs real-time monitoring, investigation, analysis, reporting and escalations of security events from multiple sources including events like: Network intrusion detection, Host based intrusion detection, Firewall logs, etc.
• Tracing, reporting and escalating malicious activity such as policy violations, Malware etc., lifecycle from end-to end.
• Perform network & host security event monitoring of alerts originating from Security Information Management (SIEM) tool & Intrusion Detection System (IDS).
• Act as the first point of contact for security incidents and requests.
• Actively contribute to the continual development of the SOC.
The Desirables...
• Any certification like CCNA, MCSE, MCP, CEH would be preferable.
• Experience with Forensic Incident Response Triage
• Exposure to SOAR technology/tools
___________________________________________________________________________
Job Title
Web Developer
Required Skills
• Build websites Using HTML5/CSS3/jQuery/JS, PHP with my sql, asp.net.
• Understanding of the entire web development process (design, development and deployment).
• Document Project Build and Maintenance.
• Candidate must have a strong understanding of Development and Debugging Tools for Cross-Browser compatibility, general web functions and standards.
• Write and Maintain Web Applications
• Deep functional knowledge or hands on design experience with Web Services is needed to be successful in this position.
• Experience with Git and GitHub.
• Experience with Photoshop.
• Familiar with Social Media and Third-Party APIs.
• Knowledgeable of Web Application Development Frameworks.
• Proficient with JavaScript.
• WordPress, Theming, and Module Development Experience, type of CMS.
• secure, acceleration of website.
The Desirables…
• knowledge of website development, Linux system including different DBMS are preferable.
• Demonstrable ability to discover and fix errors in code.
How to Apply -
If you meet the above job requirements, send your CV to support.nc@moi.gov.af. Please indicate the job title in the e-mail subject line. Any application without job title will not be considered. Also, please do not send additional documents.